Table of Contents
2013.12.23 - christmas security
i got interested in how does wireless HID devices do work. Logitech Unify system has been put on the table. quick browsing forums mentions AES, which is nice. however quick search for more exact information on the producer's site came up unifying overview document. where we can read general, yet interesting pieces of information…
encryption... or is it?
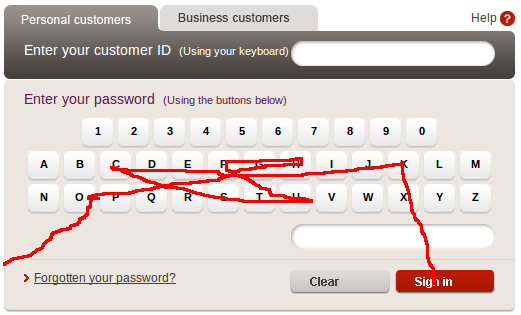
first of all, producer does not assume mouse movements are relevant, thus only wireless keyboard signal is encrypted! quite a weird assumption, taking into account that quite a few services offer mouse-entered password. banks do that for start. this is mainly meant to fool keyloggers, but since your wireless connection is NOT encrypted, you actually transfer your password in the air… what do you think the password is?
oh – and btw! you have mouse clicks as well, so it gets even simpler. and what about the image? well – forgetting about emission security issues for a second, you can gather these data from the network. connection to bank is encrypted, but the HTTP header is not, thus one can easily enter the same site victim did a second ago and just apply mouse movements. since to sniff you are probably nearby, it is very likely that you are in the same network: wired or wireless – doesn't matter much at this point.
MitM?
but it get worse – if mouse movement is not encrypted, what is the problem with remotely moving someone's mouse cursor? now that looks awfully bad…
mom - where do keys come from?
reading on Logitech's description we see that new devices are pre-paired with the receivers. this means you can just plug and play it. nice and more less secure – assuming keys are not stored/stolen by someone within the factory, or the company itself. NSA would love it i guess.
but let's assume this is not the case here1). so how about pairing new device(s)? Logitech claims single receiver can handle up to 6 of them. well – this is done by software. user can choose to connect new device, and keys are generated and stored in the hardware. the funny part is AES is a symmetric encryption. luckily the key is not transferred in a plain-text. unfortunately instead of it, […] The same unique key is constructed both in the keyboard and in the receiver based on random values exchanged during the pairing procedure. […]. does anyone else smell security-by-obscurity approach here? what it means is that it's enough to reverse-engineer the algorithm within any device to by able to get your hands on all keys.
since an exchange of pseudo-random numbers is done in a plain-text as well, MitM on a key generation phase can probably be done as well.
possible improvements
first of all – encrypt everything. what's the point of not encrypting mouse events, it it's already done for keyboards?
it would also be nice to generate some random noise here and there to achieve better privacy (eavesdropper would never know which transmission is an action and which is noise). this would not require great deal of battery life-time.
pairing is done just plain(-text) wrong. why not use certificates? Logitech could generate root-CA for their devices, sign each device's certificate with it and upload into each device. then only logitech-approved device could connect (i.e. would offer a valid certificate) and these certificates could be used for doing safe communication. by showing certificate number, device could be verified by the user, to ensure this is indeed her device that is trying to pair. this model could be used to do either all of the communication securely or at least for a key exchanging phase (symmetric encryption requires less computational power than asymmetric).
conclusion
mechanically device is smooth and handy. nice at the first sight, but not so secure if you get into details. strong encryption algorithms are good, but they need to be used wisely. we're in XXI century for haven's sake.
day by day i'm more and more convinced that there should be at least one security expert in each branch in the industry and no product should be sold w/o passing a full-scale review of its security aspects. until that happens i think i prefer wired and/or open-source-based solutions, so that either there will be no easy attack vector, or i would have a chance to fix broken-by-design elements of a purchased system.